As public safety agencies continue to modernize their technology, one concern consistently rises to the top: security. Records Management Systems (RMS) store some of the most sensitive data in law enforcement, from criminal justice information (CJI) to personally identifiable information. Protecting that data is not optional—it is mission-critical.
At the same time, many agencies are transitioning from on-premise systems to cloud-based RMS platforms. While this shift offers significant operational advantages, it also raises important questions about compliance, risk, and data protection.
Understanding security standards like CJIS and SOC 2 is a key part of evaluating any modern RMS solution. But compliance alone is not the full picture. Today’s agencies need to look beyond certifications and focus on how security is implemented in real-world environments.
Why Security Software Standards Matter
RMS platforms sit at the core of public safety operations. They store incident reports, arrest records, case data, and other sensitive information that agencies rely on every day.
A security breach in an RMS system can have serious consequences, including operational disruption, legal exposure, and damage to public trust. For that reason, agencies must ensure that their systems meet strict security and compliance standards.
Security is no longer just an IT concern—it is a critical factor in selecting and maintaining the systems that support daily operations.
Understanding CJIS Compliance
The Criminal Justice Information Services (CJIS) Security Policy, managed by the FBI, sets the standard for how criminal justice information must be handled, stored, and transmitted.
Any RMS that processes or stores CJI must comply with CJIS requirements. These standards are designed to ensure that sensitive data is protected at every level of the system.
CJIS compliance includes several critical safeguards, such as:
- Strong encryption for data both at rest and in transit
- Multi-factor authentication for secure system access
- Strict access controls to limit data visibility to authorized personnel
- Comprehensive audit logging to track system activity and detect issues
In addition, CJIS policies extend beyond technology to include personnel requirements, such as background checks for individuals with access to sensitive systems.
For agencies, CJIS is not optional—it is the baseline requirement for operating securely within the law enforcement ecosystem.
What SOC 2 Type II Certification Means
While CJIS focuses specifically on criminal justice data, SOC 2 certification provides a broader framework for evaluating how organizations manage and protect customer data.
Developed by the American Institute of Certified Public Accountants (AICPA), SOC 2 is based on five key principles: security, availability, processing integrity, confidentiality, and privacy.
There are two types of SOC 2 reports. Type I evaluates whether security controls are properly designed at a specific point in time. Type II goes further by assessing how those controls perform over an extended period.
For public safety agencies, SOC 2 Type II certification offers an added level of assurance. It demonstrates that a vendor not only has the right controls in place but is consistently operating them effectively over time.
What Modern RMS Security Requires
While CJIS and SOC 2 are essential, they represent only part of a comprehensive security strategy. Modern RMS platforms must go beyond compliance to address evolving cybersecurity threats.
This includes implementing a range of advanced security measures, such as:
- Secure, government-grade cloud infrastructure to protect sensitive data
- Continuous monitoring and threat detection for real-time risk identification
- Regular vulnerability testing to identify and address system weaknesses
- Data redundancy and disaster recovery to ensure operational continuity
- Role-based access controls and least-privilege models to minimize exposure
In today’s environment, security is not a one-time implementation—it is an ongoing process that requires constant attention and adaptation.
Common Misconceptions About the Cloud
Despite advancements in cloud technology, some agencies still hesitate to move away from on-premise systems due to concerns about security. A common misconception is that cloud-based systems are inherently less secure. In reality, the opposite is often true.
On-premise systems frequently rely on aging infrastructure, inconsistent patching, and limited monitoring capabilities. These environments can introduce significant vulnerabilities, especially as cyber threats become more sophisticated.
Cloud-based RMS platforms, when properly implemented, benefit from enterprise-level infrastructure, continuous updates, and dedicated security resources. This often results in a stronger overall security posture compared to traditional on-premise systems.
The real risk is not adopting cloud technology—it is continuing to rely on outdated systems that may no longer meet modern security standards.
What to Look for in a Secure Cloud RMS
When evaluating a cloud-based RMS, agencies should look for more than just basic compliance claims.
A secure solution should include key features such as:
- CJIS compliance to meet mandatory law enforcement security standards
- SOC 2 Type II certification to demonstrate ongoing control effectiveness
- Secure cloud hosting, ideally within government-focused environments
- Built-in audit trails and comprehensive logging capabilities
- Robust access controls to manage user permissions effectively
- Disaster recovery and uptime guarantees to maintain operational continuity
- Regular updates and proactive patch management to address emerging threats
Selecting a solution with these capabilities helps ensure long-term security, reliability, and compliance.
ARMS Delivers a Secure & Compliant RMS
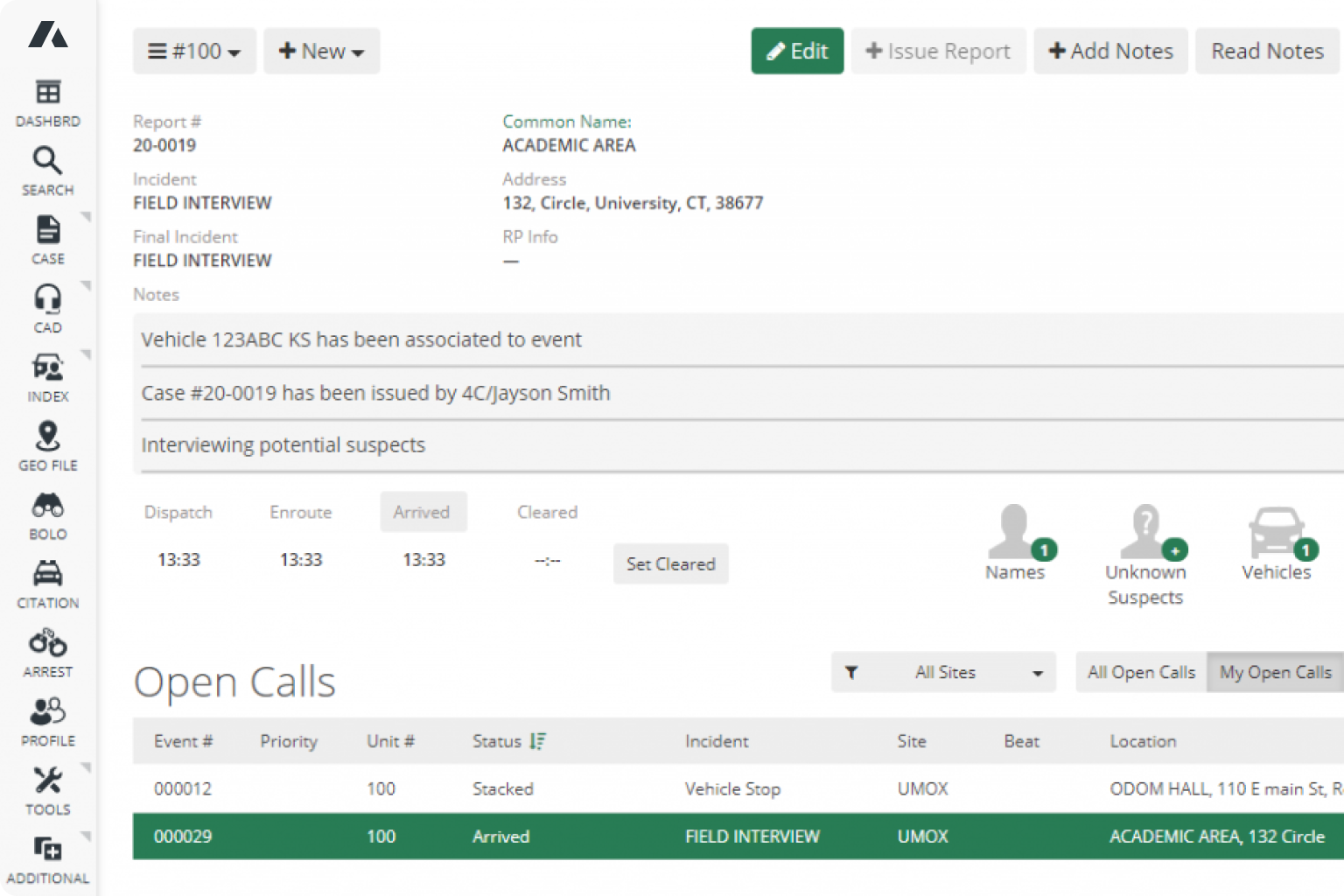
ARMS is designed to meet the security and compliance needs of modern public safety agencies. Built on a secure, cloud-based infrastructure, ARMS supports CJIS compliance requirements while providing the safeguards necessary to protect sensitive data.
Hosted on Microsoft Azure Government, ARMS SaaS leverages a highly secure environment designed specifically for public sector organizations. Built-in features such as multi-factor authentication, role-based access controls, and comprehensive audit logging help ensure that data is protected and accessible only to authorized users.
In addition, ARMS supports business continuity through reliable backup and disaster recovery capabilities, helping agencies maintain operations even in unexpected situations.
By delivering continuous updates and reducing the burden of managing on-premise infrastructure, ARMS enables agencies to strengthen their security posture while improving operational efficiency.
Security is More Than a Checkbox
Security in public safety technology is not static. It is an ongoing responsibility that requires both strong foundational standards and continuous improvement.
While CJIS compliance and SOC 2 certification provide essential benchmarks, agencies must look beyond these frameworks to ensure their systems are truly secure in practice.
Modern cloud-based RMS solutions, when properly implemented, offer a powerful combination of compliance, resilience, and scalability. For agencies looking to reduce risk and improve operational reliability, investing in secure, cloud-based technology is a critical step forward.
Ready to strengthen your agency’s security and compliance strategy? Contact ARMS today to learn how our cloud-based RMS solution can support your needs.