User Access Permissions are the fundamental security settings that determine which parts of a system a user can access and modify. Think of them as keys that unlock different areas of your organization’s software—they control not just who can see information but also who can edit or remove it.
In environments handling sensitive public safety data, ensuring that users only access what they absolutely need is critical. Poorly managed permissions can lead to data breaches, unauthorized modifications, and compliance violations—all of which can put your system’s integrity at risk.
The Risks of Poor User Access Management
The most common security failures start with access control issues, where users have more permissions than they need. These are some of the most significant risks:
1. Over-Privileged Accounts
- When users have unnecessary administrative privileges, they can accidentally—or intentionally—modify, delete, or leak sensitive data.
- A disgruntled employee or a careless mistake can expose critical records or disrupt operations.
- Even if the data remains intact, unauthorized access can result in activity that organizations never intended or expected.
2. Real-World Example: The Verkada Breach
In 2020, Verkada, a security camera company, suffered a catastrophic breach exposing 150,000 live video feeds, including footage from police departments and jails.
What Happened?
Hackers gained access through compromised admin-level credentials, allowing them to view and control security cameras across multiple organizations.
The Consequences:
- The breach led to a $3 million SEC fine.
- Police departments and other clients lost trust in Verkada’s security infrastructure.
- The company suffered severe reputational damage and increased regulatory scrutiny.
Lesson Learned: Had Verkada followed strict access management principles, such as limiting admin-level access and implementing multi-factor authentication, the breach could have been prevented.
Best Practices for Managing User Permissions
To mitigate risks and prevent breaches, organizations must follow strong access control practices. Here are the key strategies:
1. Apply the Principle of Least Privilege (PoLP)
This principle states that users should only have access to the minimum permissions necessary to perform their job—no more, no less.
- Regularly review and adjust permissions as employees change roles.
- Restrict admin-level access to only essential personnel.
- Use temporary elevated access for specific tasks instead of permanent admin permissions.
2. Conduct Regular Access Audits
Organizations should periodically review user access to ensure:
- No unauthorized users have lingering access to sensitive systems.
- Former employees or contractors no longer have access.
- Privileged accounts are appropriately monitored and limited.
💡 Pro Tip: Schedule quarterly audits to catch and correct permission errors before they become vulnerabilities.
3. Enforce Multi-Factor Authentication (MFA)
Passwords alone are not enough—compromised credentials are one of the leading causes of security breaches. Implementing Multi-Factor Authentication (MFA) ensures that only the right people can access critical systems.
- Require two-step authentication for admin accounts.
- Use email, SMS, or authentication apps to verify logins.
- Prevent unauthorized logins even if passwords are leaked.
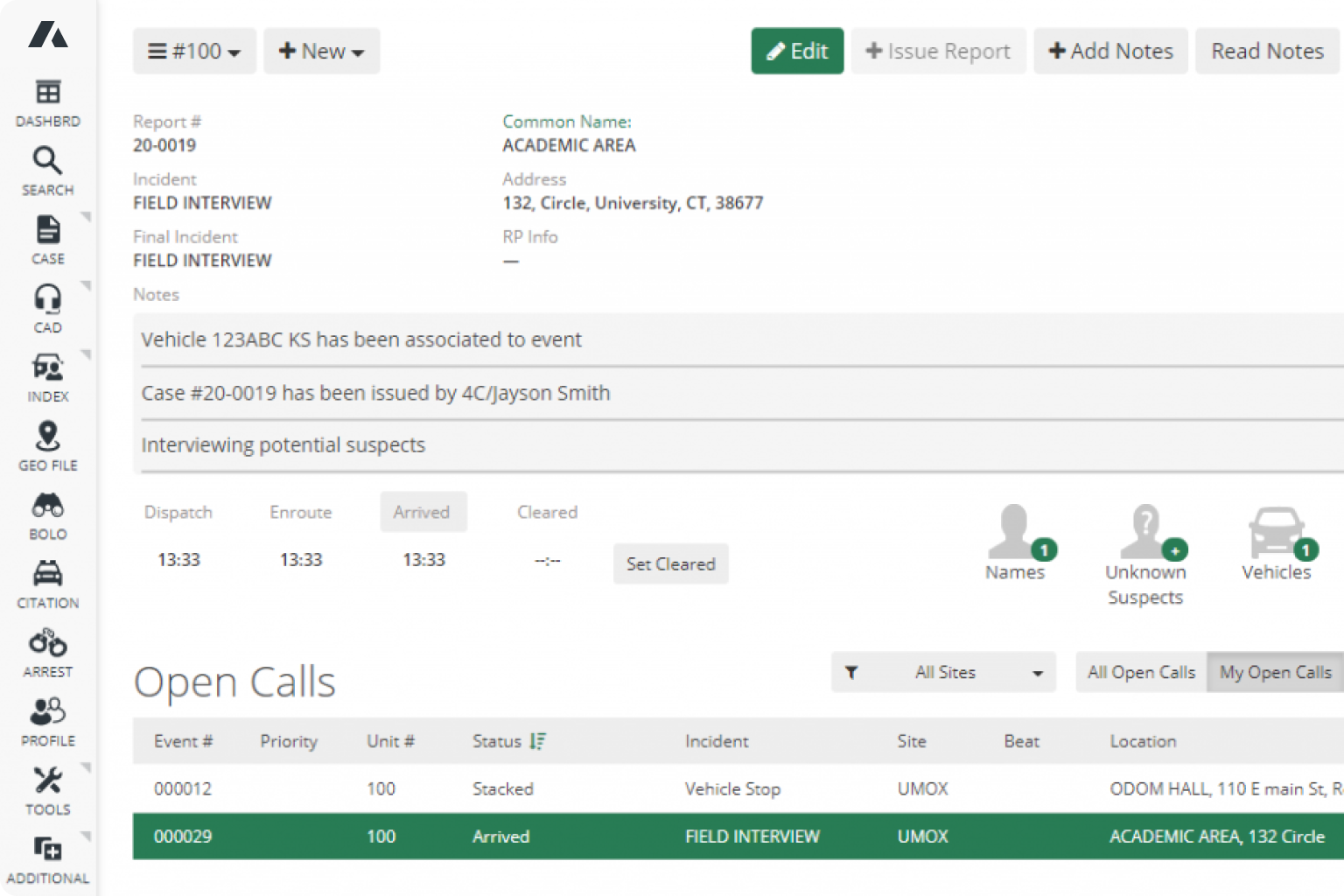
How ARMS Simplifies User Access Management
ARMS provides built-in reporting tools to streamline and secure User Access Permissions.
1. Permission Templates for Role-Based Access
Instead of manually assigning permissions, ARMS lets you organize permissions into reusable templates.
- Assign predefined roles to users based on their job function.
- Easily clone permissions for new employees.
- Maintain consistency in security settings across your organization.
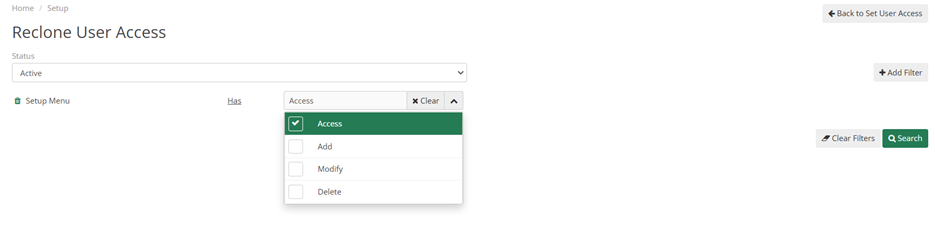
2. “Reclone” Function for Bulk Updates & Audits
ARMS makes it easy to audit and adjust permissions in real-time.
- View who has access to specific system areas at a glance.
- Bulk update permissions to enforce security policies.
- Quickly correct over-privileged accounts with a few clicks.
🔎 Example: If an employee moves from dispatch to patrol, you can instantly reassign the correct permission set—ensuring they no longer have access to unnecessary data.
Compliance & Regulatory Benefits
Proper User Access Management is not just about security—it’s also required for agencies handling sensitive information.
- For Law Enforcement Agencies: ARMS’ access controls help meet CJIS Security Policy standards for handling criminal justice data.
- For Agencies Handling Medical Data: ARMS ensures compliance with HIPAA regulations by restricting access to health-related records.
- For Government & Public Safety Organizations: ARMS supports FISMA compliance, ensuring federal security requirements are met.
Why This Matters: Failure to comply with these standards can result in fines, data exposure, and legal liability.
Secure Your Data Before It’s Too Late
Every day, organizations suffer security breaches—some minor, others catastrophic. Proactive User Access Management can save your agency time, money, and legal headaches.
By implementing best practices like PoLP, regular audits, and MFA, you reduce risk and strengthen your organization’s security posture. And with ARMS’ built-in tools, managing user permissions is simple, scalable, and fully compliant with industry regulations.
Don’t wait for a breach to happen—start securing your data today with ARMS!